Warning!!! Crypto Trust Wallet Extension 2.68 HACKED on 12/25/25. Do NOT Open your Trust Wallet browser wallet EXTENSION, for now.
Did you ever get your crypto stolen? Here’s probably how it happened. Check out my WordPress post for How to stay Secure while using your Crypto Wallet: https://propheticmoney.com/did-you-ever-get-your-crypto-stolen-here-is-what-happened-prophetic-money/
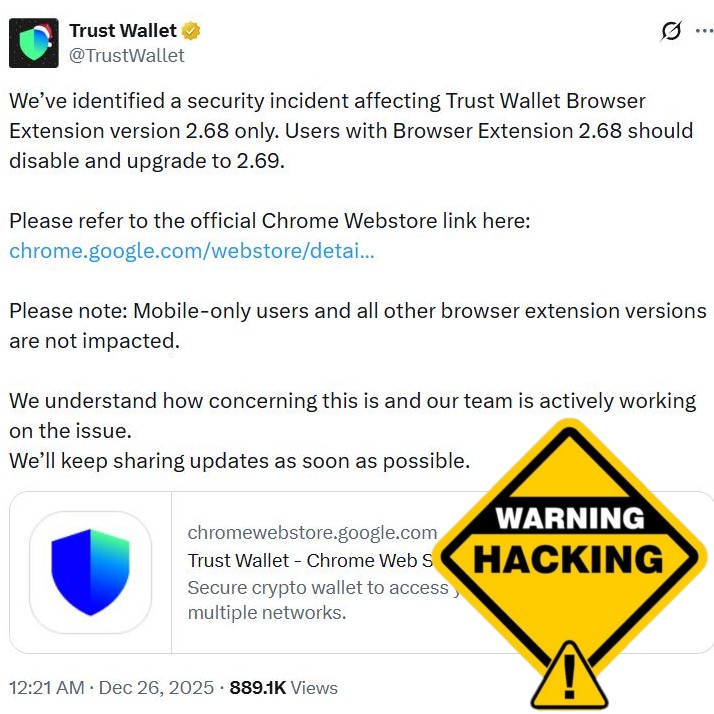
Trust Wallet official twitter post evening of 12/25/25:
https://x.com/TrustWallet/status/2004316503701958786
Trust Wallet @TrustWallet 12/25/25
We’ve identified a security incident affecting Trust Wallet Browser Extension version 2.68 only. Users with Browser Extension 2.68 should disable and upgrade to 2.69.
Please refer to the official Chrome Webstore link here: https://chrome.google.com/webstore/detail/trust-wallet/egjidjbpglichdcondbcbdnbeeppgdph
Please note: Mobile-only users and all other browser extension versions are not impacted.
We understand how concerning this is and our team is actively working on the issue.
We’ll keep sharing updates as soon as possible.
chromewebstore.google.com
We’ve identified a security incident affecting Trust Wallet Browser Extension version 2.68 only. Users with Browser Extension 2.68 should disable and upgrade to 2.69.
— Trust Wallet (@TrustWallet) December 25, 2025
Please refer to the official Chrome Webstore link here: https://t.co/V3vMq31TKb
Please note: Mobile-only users…
https://x.com/TrustWallet/status/2004355490734919980
Trust Wallet @TrustWallet 12/25/25
For users who haven’t already updated to Extension version 2.69, please do not open the Browser Extension until you have updated. This may help to ensure the security of your wallet and prevent further issues.
For users who haven't already updated to Extension version 2.69, please do not open the Browser Extension until you have updated. This may help to ensure the security of your wallet and prevent further issues.
— Trust Wallet (@TrustWallet) December 26, 2025
https://x.com/TrustWallet/status/2004381562377527702
Trust Wallet @TrustWallet 12/25/25
Follow the step-by-step guide soonest possible:
Step 1: Do NOT open the Trust Wallet Browser Extension on your desktop device to ensure the security of your wallet and prevent further issues.
Step 2: Go to Chrome Extensions panel in your Chrome browser by copying following to the address line (shortcut to the Official Trust Wallet Browser Extension): chrome://extensions/?id=egjidjbpglichdcondbcbdnbeeppgdph
Step 3: Switch the toggle to “Off” below the Trust Wallet if it’s still “On”.
Step 4: Click “Developer mode” in the upper right corner.
Step 5: Press the “Update” on the left upper corner.
Step 6. Check the version number: 2.69. This is the latest and secure version.
Follow the step-by-step guide soonest possible:
— Trust Wallet (@TrustWallet) December 26, 2025
Step 1: Do NOT open the Trust Wallet Browser Extension on your desktop device to ensure the security of your wallet and prevent further issues.
Step 2: Go to Chrome Extensions panel in your Chrome browser by copying following to…
https://x.com/TrustWallet/status/2004340002776555742
Trust Wallet @TrustWallet 12/25/25
Our Customer Support team is already in touch with impacted users regarding next steps. Please ask those in your DM to reach out to our Support team here: https://twtholders.trustwallet.com
Our Customer Support team is already in touch with impacted users regarding next steps. Please ask those in your DM to reach out to our Support team here: https://t.co/MN6V2oL4Yf
— Trust Wallet (@TrustWallet) December 25, 2025
https://x.com/TrustWallet/status/2004475085168795941
Trust Wallet @TrustWallet 12/26/25
Update on the Trust Wallet Browser Extension (v2.68) incident:
We’ve confirmed that approximately $7M has been impacted and we will ensure all affected users are refunded.
Supporting affected users is our top priority, and we are actively finalizing the process to refund the impacted users. We appreciate your patience and will share instructions on next steps soon.
Please do no interact with any messages that do not come from our official channels.
Update on the Trust Wallet Browser Extension (v2.68) incident:
— Trust Wallet (@TrustWallet) December 26, 2025
We’ve confirmed that approximately $7M has been impacted and we will ensure all affected users are refunded.
Supporting affected users is our top priority, and we are actively finalizing the process to refund the… https://t.co/2XRx8GvZ75
https://x.com/cz_binance/status/2004397190819783013
CZ BNB @cz_binance 12/26/25
So far, $7m affected by this hack. @TrustWallet will cover. User funds are SAFU. Appreciate your understanding for any inconveniences caused.
The team is still investigating how hackers were able to submit a new version.
So far, $7m affected by this hack. @TrustWallet will cover. User funds are SAFU. Appreciate your understanding for any inconveniences caused.
— CZ BNB (@cz_binance) December 26, 2025
The team is still investigating how hackers were able to submit a new version. https://t.co/xdPGwwDU8b
https://x.com/EowynChen/status/2004649284537647161
Eowync.eth @EowynChen 12/26/25
I want to share a transparent update on the @TrustWallet
Browser Extension v2.68 security incident, and what we know so far ~24 hours of the attack.
This is an ongoing investigation, so I’ll focus on confirmed facts and updates, highly likely hypothesis, and what we’re doing to stop loss for users.
The scope of impact from our investigation confirms that this security incident affects:
- Only Browser Extension version 2.68 users who opened the extension and logged in
It does NOT affect:
- Any mobile app users
- Any other versions of browser extension users
- Extension v2.68 users who opened and logged in after Dec 26, 2025 1100 UTC.
What we know:
The malicious extension v2.68 was NOT released through our internal manual process. Our current findings suggest it was most likely published externally through Chrome Web Store API key, bypassing our standard release checks.
A working hypothesis (still under investigation):
The hacker used a leaked Chrome Web Store API key to submit the malicious extension version v2.68. This successfully passed Chrome Web Store’s review and was released on Dec 24, 2025 at 12:32 UTC.
To minimize impact to users, we took the following steps:
1) We reported the malicious domain to the registrar, NiceNIC, and it has been suspended. Even for users still on Extension v2.68, there should be no risk of further loss.
2) We expired all release APIs – no new releases possible for the next 2 weeks.
3) We start actively collecting victims’ tickets and processing reimbursement. Some details still hashing out.
There’s still much to be done: Internal forensic analysis is ongoing and we are awaiting a response from Google’s support team for additional logs to further analyze root cause – the holiday season makes it a bit challenging to get a timely response, so please bear with us
We are trying to do the right thing for our users. We will share a full post-mortem once we have verified findings from pending audit logs and investigations, and continue to tighten security operations and controls.
Protecting users is always our priority. We will learn and rise from this, and do better. We greatly appreciate your patience and continued support.
And a big thank you to the security community for the support and monitoring;
@ZachXBT, @samczsun, @AndrewMohawk, @pcaversaccio, @vikmeup, @tayvano_ , @0xakinator , @chainalysis, @arkham, and many more whitehat hackers!
I want to share a transparent update on the @TrustWallet Browser Extension v2.68 security incident, and what we know so far ~24 hours of the attack.
— Eowync.eth (@EowynChen) December 26, 2025
This is an ongoing investigation, so I’ll focus on confirmed facts and updates, highly likely hypothesis, and what we’re doing to…
https://x.com/TrustWallet/status/2004623205005492651
Trust Wallet @TrustWallet 12/26/25
Update on Trust Wallet Browser Extension v2.68 Security Incident: Compensation Process
To start the compensation process, affected users should please complete this form: https://be-support.trustwallet.com to help us process your case.
Our support team is prioritizing all the victims from the incident and has already begun reviewing submissions.
We apologize and acknowledge that this situation has been frustrating and disruptive. We are working around the clock to finalize the compensation process details and each case requires careful verification to ensure accuracy and security.
We will be in close contact with the victims on any progress and updates. We appreciate your patience with us.
Update on Trust Wallet Browser Extension v2.68 Security Incident: Compensation Process
— Trust Wallet (@TrustWallet) December 26, 2025
To start the compensation process, affected users should please complete this form: https://t.co/xlBLrL6kMj to help us process your case.
Our support team is prioritizing all the victims from… https://t.co/yaqFNLxuyx
https://x.com/SlowMist_Team/status/2004505097049628846
SlowMist @SlowMist_Team 12/26/25
A diff comparison between v2.67 and v2.68 revealed malicious code secretly inserted into the 2.68 update. This injected code iterates through all wallets stored in the extension, triggering a get mnemonic phrase request for each wallet. The encrypted mnemonic is then decrypted using the password or passkeyPassword entered during wallet unlock.
🕸️Once decrypted, the mnemonic phrase is sent to the attacker’s server: api.metrics-trustwallet[.]com
👁️Further analysis of domain information shows that the attacker used the domain metrics-trustwallet[.]com was registered on 2025-12-08 02:28:18 (registrar: NICENIC INTERNATIONAL). Network records indicate the first requests to api.metrics-trustwallet[.]com began on 2025-12-21, which aligns with the code backdoor insertion time on Dec 22.
A diff comparison between v2.67 and v2.68 revealed malicious code secretly inserted into the 2.68 update. This injected code iterates through all wallets stored in the extension, triggering a get mnemonic phrase request for each wallet. The encrypted mnemonic is then decrypted… pic.twitter.com/HdxLQd5eq8
— SlowMist (@SlowMist_Team) December 26, 2025
https://x.com/SlowMist_Team/status/2004505108407636055
SlowMist @SlowMist_Team 12/26/25
Mitigation Recommendations🛡
🔹If you have ever installed the Trust Wallet browser extension, immediately disconnect your device from the network before performing any investigation or operations.
🔹Export your private key/mnemonic phrase immediately and uninstall the Trust Wallet browser extension.
🔹After backing up the mnemonic/private key, quickly transfer your funds to another secure wallet.
📄 Full detailed analysis by SlowMist: https://slowmist.medium.com/christmas-heist-analysis-of-trust-wallet-browser-extension-hack-bdb35c3cc6dd
Mitigation Recommendations🛡
— SlowMist (@SlowMist_Team) December 26, 2025
If you have ever installed the Trust Wallet browser extension, immediately disconnect your device from the network before performing any investigation or operations.
Export your private key/mnemonic phrase immediately and uninstall the Trust…
https://x.com/EowynChen/status/2005042356773638157
Eowync.eth @EowynChen 12/27/25
Browser Extension Incident – Short Update (Dec 27)
Sharing another update on where we are with the Browser Extension incident handling.
1/ Our forensic investigation is ongoing. Google replied saying it has escalated our ticket – good news! We hope to receive the Chrome Store audit logs soon. Also devices from remote workers are en route to our security team for more detailed checks. This will take some shipping time despite being expedited.
2/ Our Extension now prompts affected users—if compromised wallets are detected on the device – users are urged to migrate and abandon old wallets immediately to prevent further loss. So if you see the banner on Extension, please act immediately. If you don’t see the banner – great, you are fine and no action is required.
3/ Our priority is making sure reimbursements go to the right people. Verifying ownership while filtering out scammers and hackers is complex, so processing requests are taking longer than the affected users expected. We’re improving our tools and processes, as well as developing new Extension features to improve accuracy. Launching soon.
4/ We’ve received 2,630+ claims & reports for reimbursement — more than 10x our usual ticket volume. Losses in claims vary from $1.05 to $3.5M. Our Customer Support team is stretched a lot more than usual but they are responding to claims as quickly as possible. We are also in the process of sourcing more support capacity. Thanks for your patience.
Browser Extension Incident – Short Update (Dec 27)
— Eowync.eth (@EowynChen) December 27, 2025
Sharing another update on where we are with the Browser Extension incident handling.
1/ Our forensic investigation is ongoing. Google replied saying it has escalated our ticket – good news! We hope to receive the Chrome Store…
GROK AI Summary (12/28/25)
Trust Wallet Browser Extension v2.68 Hack (as of December 28, 2025)
Supply chain attacks on browser extensions like the Trust Wallet incident (version 2.68) are particularly nasty because they exploit trust in the official update process — users think they’re getting a legitimate improvement from a trusted company, but malicious code sneaks in somewhere along the way.
How This Specific Attack Happened (Trust Wallet v2.68 – Dec 2025)From security reports, on-chain analysis (ZachXBT, SlowMist, MistTrack), code comparisons (v2.68 vs. v2.69), and the latest forensic details:
- Malicious code injection
- A seemingly innocent JavaScript file (referred to as 4482.js or variants like 8423.js in diffs) was modified/added in v2.68 (released ~Dec 24, 2025).
- It masqueraded as “analytics” or metrics tracking (hijacking PostHog library behavior, pointing to api.metrics-trustwallet[.]com — attacker-controlled domain registered Dec 8, 2025).
- In reality, it contained a backdoor that targeted wallet secrets.
- Trigger mechanism – the new revelation
- The code activates primarily on wallet unlock/login.
- It iterates through all stored wallets in the extension.
- When the user unlocks the wallet (by entering password or passkeyPassword), the malicious code decrypts the encrypted mnemonic/seed phrase using that input.
- The decrypted seed phrase is then immediately exfiltrated — sent to the attacker’s server via the “errorMessage” field in disguised analytics requests (confirmed by SlowMist’s traffic analysis and code reproduction).
- SlowMist explicitly describes: “When the wallet is unlocked, the attacker obtains the password or passkeyPassword, then calls GET_SEED_PHRASE to retrieve the wallet’s mnemonic phrase… and then places the mnemonic phrase into the ‘errorMessage’.”
- This explains why many victims saw near-instant drains after interacting with the extension post-update.
- Important nuance: While seed phrase import was an early suspected vector (and still risky), the confirmed primary mechanism is unlock/login exposing already-stored encrypted mnemonics. Passive installation or simple opening without unlocking does not appear to trigger exfiltration (no evidence in reports or victim patterns). Early broad warnings to “avoid opening” were precautionary.
- How the code got in (supply chain part)
Several realistic scenarios — investigation ongoing (forensics, Google audit logs escalated, remote worker devices under review as of Dec 27):
| Scenario | How it works | Likelihood / Notes |
| Developer account compromise | Phished/stolen credentials/OAuth tokens → direct upload to Chrome Web Store | Very high – common in 2024/2025 attacks |
| Build pipeline / CI/CD hack | Breach of build server, repo, or dependencies → injection during packaging | High – classic vector |
| Dependency/submodule poisoning | Malicious code in third-party JS library | Medium – less evidence here |
| Insider / rogue employee | Intentional addition by someone with access | Low – no indication so far |
SlowMist concludes this is likely a professional APT-level attack with prior access to dev environments (not simple npm poisoning).
Why It’s Called a “Supply Chain” Attack
You update from the official Chrome Web Store — the most trusted source. Yet the software is poisoned between developers and your browser. Auto-updates silently delivered the backdoor to potentially hundreds of thousands of users.
Latest Status (as of Dec 28, 2025)
- Affected scope: Only v2.68 users who unlocked/logged in before Dec 26, 2025, 11:00 UTC. Post-fix unlocks safe (domain suspended). Mobile apps & other versions unaffected.
- Losses: $7M total ($3M BTC, $3M+ ETH/L2, minor SOL). Funds laundered via exchanges & bridges.
- Response: v2.69 (Dec 25/26) removes the code; includes safety banner for detection.
Compensation: 2,600+ claims received; Binance-backed full reimbursement ongoing (CZ confirmed SAFU). Submit via official Trust Wallet form only — beware scams. - Investigation: Root cause still pending; no new details since Dec 27.
Bottom line for users right now
- If you ever unlocked/logged in to v2.68 (or imported a seed) before the cutoff → assume your seed phrase is compromised.
- Immediately: Export keys securely (offline/air-gapped if possible), uninstall v2.68, create a new wallet (ideally hardware like Ledger/Trezor), transfer any remaining funds.
- Browser extensions remain high-risk in 2025 — treat them as untrusted, verify every update, minimize exposure, and prefer hardware/self-custody for serious holdings.
Stay updated via @TrustWallet, @EowynChen, or @SlowMist_Team official channels. Stay safe out there!