Did you know you can check if you have an email address or password that has been compromised in a data breach?
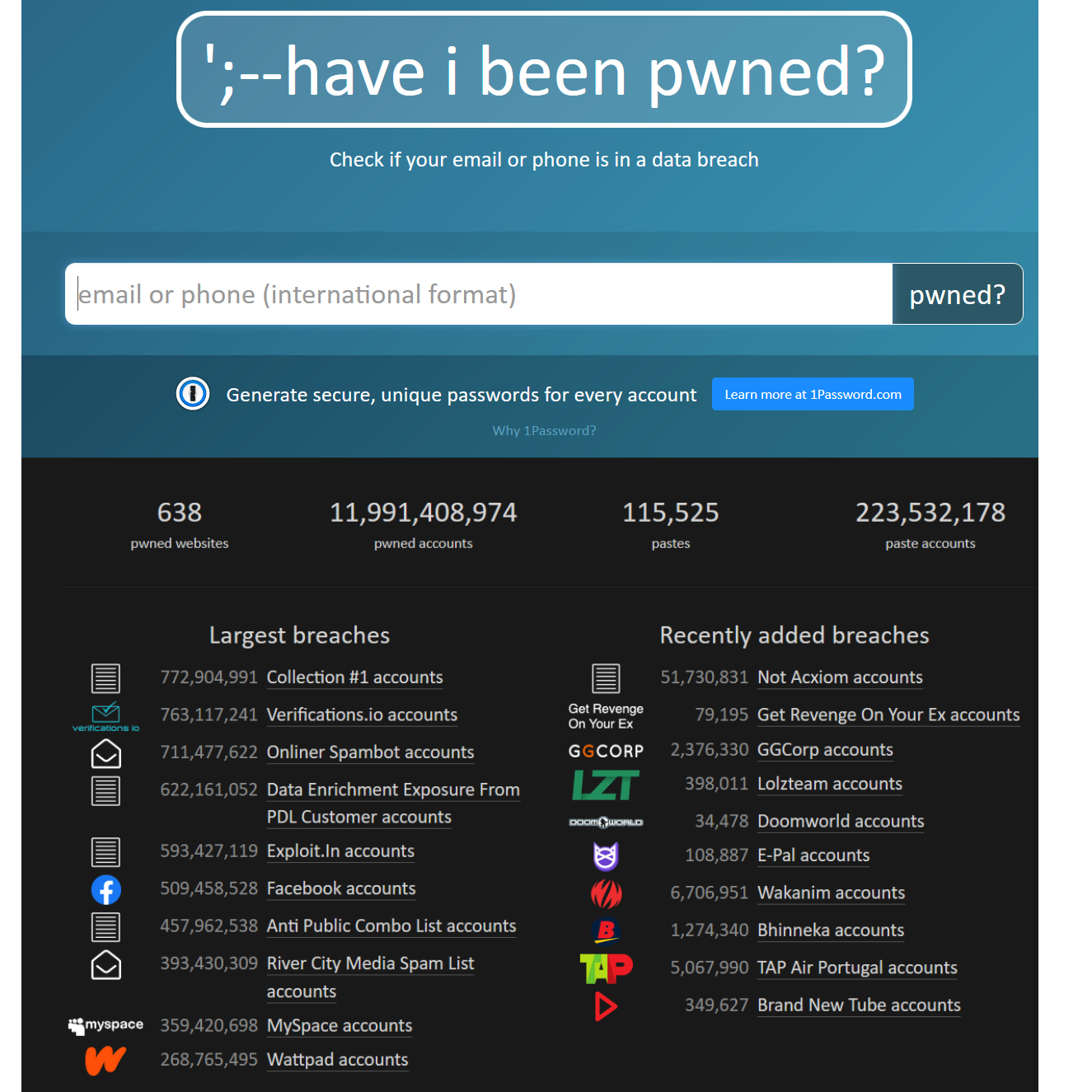
‘;–have i been pwned? – is a very popular and very old website that allows people to do this for free.
For the more advances/technical users, who use the keepass password manager. They can download the entire haveibeenpwned database and use keepass to check if any information is present. This is done in seconds, as opposed to having to type in every single email/password you have ever used.
https://twitter.com/haveibeenpwned
NIST’s guidance: check passwords against those obtained from previous data breaches
The Pwned Passwords service was created in August 2017 after NIST released guidance specifically recommending that user-provided passwords be checked against existing data breaches . The rationale for this advice and suggestions for how applications may leverage this data is described in detail in the blog post titled Introducing 306 Million Freely Downloadable Pwned Passwords. In February 2018, version 2 of the service was released with more than half a billion passwords, each now also with a count of how many times they’d been seen exposed. A version 3 release in July 2018 contributed a further 16M passwords, version 4 came in January 2019 along with the “Collection #1” data breach to bring the total to over 551M. Version 5 landed in July 2019 with a total count of 555M records, version 6 arrived June 2020 with almost 573M then version 7 arrived November 2020 bringing the total passwords to over 613M. The final monolithic release was version 8 in December 2021 which marked the beginning of the ingestion pipeline utilised by law enforcement agencies such as the FBI.
https://haveibeenpwned.com/Passwords
P.S. This is not financial/technical advice. Just sharing my experience and opinions.