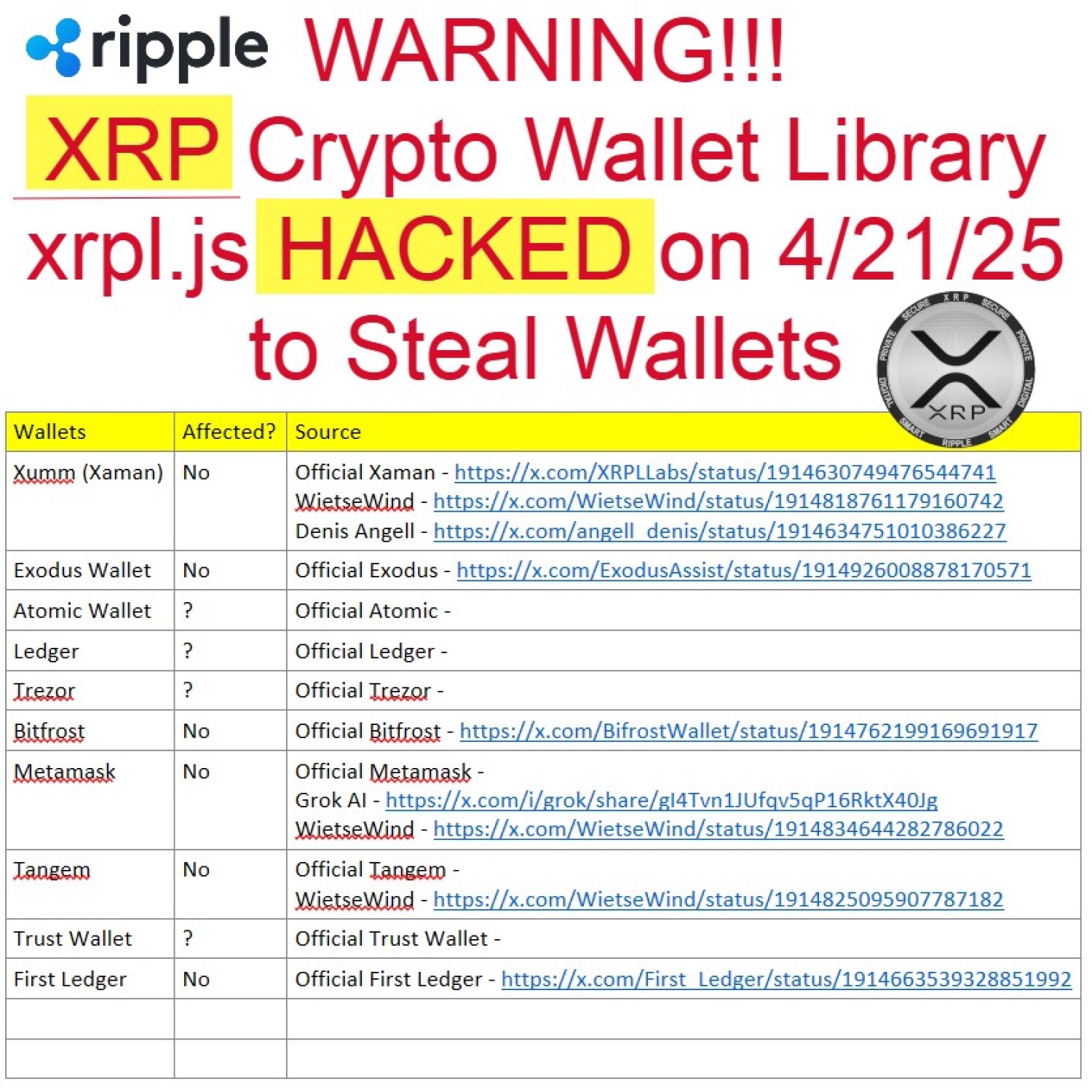
WARNING!!! XRP Crypto Wallet Library xrpl.js HACKED on 4/21/25 4:46 PM ET. This lets hackers steal XRP wallet seed phrases/private keys from affected wallets. Recommendation is to move your XRP crypto to a new wallet, if your wallet was affected. I will keep updating this post as more info comes in.
I asked Grok AI to generate a simple (dummied down) summary of what happened. Grok said that if you did not open your crypto wallet, create a new wallet, or import seed phrase after the update on April 21, 2025, you have nothing to worry about. Sometimes AI hallucinates/lies, so stay tuned…
Bad guys sneaked harmful code into a tool called xrpl.js, which people use to manage their XRP cryptocurrency. This code secretly sent their private keys—kind of like their crypto passwords—to the attackers, who could then steal their money. The problem was found on April 22, 2025, and a fixed version of the tool was released to stop the theft.
The users affected by this xrpl.js breach are those who recently used a tool, app, or service that relies on the compromised versions of xrpl.js (versions 4.2.1 to 4.2.4) to either create a new XRP wallet or import an existing one. These versions were uploaded to the NPM registry between 4:46 PM and 5:49 PM ET on April 21, 2025, and were only available for less than 24 hours before being removed. So, if you created or imported a wallet using a tool that updated to one of these bad versions during that short window, your wallet’s private key—basically your crypto password—might have been sent to the attackers, putting your funds at risk.
If the wallet maker updated their tool to use one of the compromised versions of xrpl.js (versions 4.2.1 to 4.2.4, which were available on April 21, 2025), your wallet’s seed—essentially your crypto password—was not automatically sent to hackers just because the update happened. The harmful code in those versions was designed to steal seeds only when the tool actively used xrpl.js to either create a new wallet or import an existing one. So, you would have needed to interact with the wallet after the update in one of these ways—like generating a new wallet, importing your seed to access your wallet, or performing certain actions that involve the seed—for the hackers to steal it.
For example, if your wallet maker updated their tool on April 21, 2025, but you didn’t open the app, create a new wallet, or import your seed after that update, your seed likely wasn’t sent to the hackers. However, if you’re unsure whether you interacted with the wallet in a way that involved the seed, or if you don’t know whether the tool used the bad xrpl.js version, the safest step is to assume your seed might be at risk and move your funds to a new wallet using a secure app like Xaman Wallet, which wasn’t affected by this breach.
https://x.com/WietseWind/status/1914818761179160742
WietseWind (@ Xaman, XRPL & Xahau) @WietseWind – 4/23/25
A little bit of background after what has been discovered today: a breach in the xrpl.js Javascript SDK, and measures taken by @XRPLLabs and all
@XamanWallet users safe.
Now let me explain what actually happened today:
Software relying on the compromised versions of xrpl.js exposed secret keys generated/entered by end users to third party compromise.
The xrpl.js package isn’t the first, and won’t be the last package in the crypto ecosystem to be the victim of such an attack: with billions at stake, libraries used by crypto wallets are prime targets.
Any software vendor claiming that “this kind of attack can never happen to them / their software” is lying. This can happen to the best of us. But we sure can do a bunch of things to try to prevent it.
So what is happening here? Almost all software users other software (that uses other software that uses other software, etc.). There’s an entire “tree” of dependencies: libraries maintained by third parties, so other builders can continue building without having to reinvent the wheel.
If malicious code makes it into one of these packages many other packages use, nasty things can happen. The xrpl.js package is one of the packages many (most) Web/Browser/dApp/Wallet implementations rely on, as it makes it fairly easy to interact with the XRP Ledger, XRPL accounts, etc. – and most importantly: sign transactions.
A malicious actor managed to sneak code into the xrpl.js package that sent generated / imported keypairs to a third party server. There they could gather a long list of generated keypairs, wait till there was actual balance on the accounts, and empty them. It’s likely this has already happened, or will still happen in the future.
If you have recently generated an account / keypair / secret with xrpl.js or a wallet/tool that relies on it, consider your account unsafe and please send your funds to a new account
https://www.bleepingcomputer.com/news/security/ripples-recommended-xrp-library-xrpljs-hacked-to-steal-wallets/
Ripple’s recommended XRP library xrpl.js hacked to steal wallets
By Lawrence Abrams
April 22, 2025
The recommended Ripple cryptocurrency NPM JavaScript library named “xrpl.js” was compromised to steal XRP wallet seeds and private keys and transfer them to an attacker-controlled server, allowing threat actors to steal all the funds stored in the wallets.
Malicious code was added to versions 2.14.2, 4.2.1, 4.2.2, 4.2.3, and 4.2.4 of the xrpl NPM package and published to the NPM registry yesterday between 4:46 PM and 5:49 PM ET. These compromised versions have since been removed, and a clean 4.2.5 release is now available that all users should upgrade to immediately.
The developers have also confirmed that the Xaman Wallet, XRPScan, First Ledger (Different from Ledger Hardware Wallet), and Gen3 Games projects were not affected by the supply chain attack.
Note: First Ledger is not the same thing as Ledger Hardware Wallet)
Xaman (Xumm) Wallet – Not Affected – https://x.com/XRPLLabs/status/1914630749476544741
The compromised xrpl.js NPM package does not affect @XamanWallet
Xaman uses in-house infrastructure and libraries developed by @XRPLLabs
We do not rely on third-party libraries like xrpl.js to handle private keys or transactions.
Xaman users are not affected
Exodus Wallet – Not Affected – https://x.com/ExodusAssist/status/1914926008878170571
Exodus does not use the mentioned package, so wallets are unaffected
Tangem – Not Affected – https://x.com/Tangem/status/1914959006579163330
this has nothing to do with the XRP Ledger itself, and it does not affect wallets like Tangem.
Ledger – Not Affected – https://x.com/Ledger_Support/status/1915030732017209571
Hey – We’ve reviewed the recent concerns surrounding Ripple’s xrpl.js NPM package, and can confirm that this package is not used in our codebase or infrastructure. There is no impact on our systems or the security of our users’ funds.